Data Bridge Start 813-279-5002 centers on trusted contact lookup as a privacy-conscious recovery tool. It combines layered defenses, encryption, and audits to protect personal data while enabling consent-based sharing. The system stresses multi-signal verification and independent corroboration to prevent single-point failures. Governance and user-centric defaults aim for autonomy and safety, with ongoing reviews. The potential for cross-channel validation raises questions about trust and implementation, leaving a practical path forward for those considering its use.
What Trusted Contact Lookup Is and Why It Matters
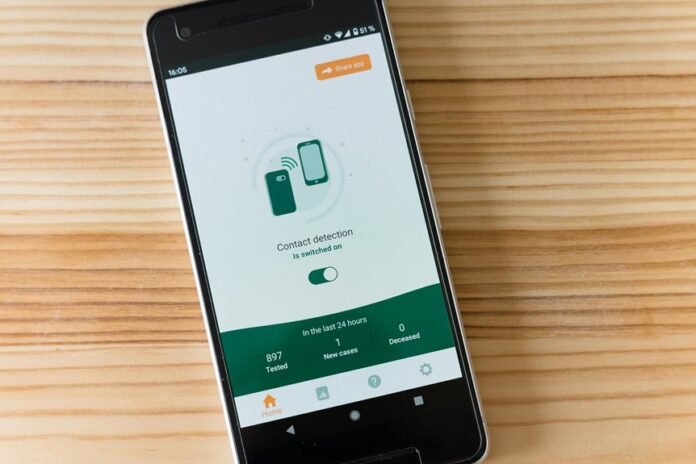
A Trusted Contact Lookup is a feature that allows an account holder to designate trusted individuals who can confirm the user’s activity or help in account recovery. The mechanism enhances lookup security by providing verified checkpoints during uncertainty, reducing unauthorized access.
It clarifies responsibilities, limits reliance on single data points, and empowers users to maintain autonomy while preserving safety and control. trusted contact, lookup security.
How Data Bridge Start 813-279-5002 Ensures Security and Privacy
Data Bridge Start 813-279-5002 prioritizes security and privacy through layered defenses and transparent practices. The system enforces security integrity via access controls, encryption, and regular audits. Privacy safeguards limit data exposure and minimize collection, maintaining user autonomy. Detected anomalies trigger swift containment, while independent reviews verify adherence. Clear governance and user-centric defaults reinforce trust without compromising freedom.
Practical Uses of Trusted Contact Lookup in Emergencies and Daily Life
They also assist daily coordination, such as secure check-ins or consent-based information sharing. Privacy safeguards and strict identity verification protect sensitive data, preserving autonomy while maintaining reliable, reachable networks for freedom-minded readers.
How to Evaluate Trustworthiness and Avoid Spoofed Identities
Evaluating trustworthiness and avoiding spoofed identities require a structured approach: verify provenance, confirm cryptographic signals, and cross-check with independent sources. Trust verification depends on transparent provenance and verifiable data. Awareness of identity spoofing reduces risk by validating moments of contact and metadata. Independent corroboration, multiple channels, and consistent signals strengthen resilience while preserving user autonomy and freedom.
Conclusion
Trusted Contact Lookup centers on consent, verification, and privacy. It offers secure, layered defenses, encryption, and audits; it provides independent corroboration, transparent provenance, and autonomy; it supports governance and user-centric defaults, with ongoing reviews. It enables reliable recovery, responsible disclosure, and cross-channel validation; it reduces single points of failure, enhances trusted restoration, and supports privacy-conscious access. It balances accessibility with safeguards, transparency with control, and usability with protection. It promises protection, precision, and prudent practices.